One Man; Many Votes
Face it. Diebold developers just write shitty code. AP (09.13.06):
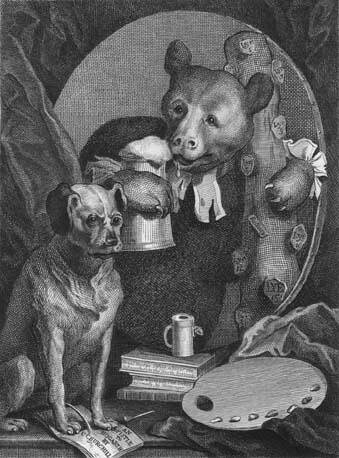
"A Princeton University computer science professor added new fuel Wednesday to claims that electronic voting machines used across much of the country are vulnerable to hacking that could alter vote totals or disable machines. In a paper posted on the university's Web site, Edward Felten and two graduate students described how they had tested a Diebold AccuVote-TS machine they obtained, found ways to quickly upload malicious programs and even developed a computer virus able to spread such programs between machines." Princeton Prof Hacks E-Vote MachineMark Radke, "(t)he marketing director for the machine's maker — Diebold Inc.'s Diebold Election Systems of Allen, Texas — blasted the report, saying Felten ignored newer software and security measures that prevent such hacking." So if the older software really sucked, what kind of confidence should we have in the newer stuff, Mark? Mark also questioned "why Felten hadn't submitted his paper for peer review, as is commonly done before publishing scientific research." Maybe Mark isn't aware that Ed's published his share of peer-reviewed papers, and is very highly regarded in the computer security field. As in if you want to go toe-to-toe with Ed, you'd better come loaded for bear. Besides. Mark is a freakin' marketing director. Even if he'd read Ed's paper, we highly doubt he'd have a clue what it was about. How bad was the older stuff? Ha! It was really, really bad. "Felten and graduate students Ariel Feldman and Alex Halderman found that malicious programs could be placed on the Diebold by accessing the memory card slot and power button, both behind a locked door on the side of the machine. One member of the group was able to pick the lock in 10 seconds, and software could be installed in less than a minute, according to the report." "The researchers say they designed software capable of modifying all records, audit logs and counters kept by the voting machine, ensuring that a careful forensic examination would find nothing wrong." "It was also possible to design a computer virus to spread malicious programs to multiple machines by piggybacking on a new software download or an election information file being transferred from machine to machine, Felten said." This is just the latest in a long line of folks who have been beating the holy hell out of Diebold's security.

0 Comments:
Post a Comment